An experience of grabbing packets for grab app
During my time in Singapore, to achieve a cashless experience, my all-currency credit card did not support UnionPay QuickPass, so I had to use a third-party platform to link my bank card.
Grab only provided BOC (Bank of China) as a third-party platform for mainland users, but after opening the link, I found that the verification code on BOC's login page couldn't be displayed.
My task was to try and troubleshoot why the verification code wasn't showing—at the very least, I needed to reproduce this URL on a computer.
Grab Desktop
Couldn't find it at all.
Android + HTTPToolkit (User Certificate)
BurpSuite doesn't seem to have particularly good support for Android, and I just found out that Fiddler is actually commercial software. So, I chose HTTPToolkit.
https://github.com/httptoolkit/httptoolkit-desktop
And the corresponding Android version:
https://github.com/httptoolkit/httptoolkit-android
HTTPToolkit allows installing two types of certificates on Android: user and system. The latter obviously requires root access.
I tried using only the user certificate and was able to capture HTTP/HTTPS packets from Chrome, but it didn't work with Grab's built-in browser.
With Nova's hint, I realized it might be due to SSL pinning. A Google search led me to this article:
https://www.secpulse.com/archives/134061.html
It suggested using the JustTrustMe module from Xposed to solve the issue, which definitely requires root.
I definitely didn't want to root my brand-new phone, so I opted for:
Waydroid + Magisk
Linux systems have to say goodbye to WSA and most Android emulators. Currently, Waydroid is a good alternative.
The official Waydroid Android 11 image doesn't come with Magisk. Although you can switch to root by running su in the shell, for convenience, I used a repository to build an image that includes GApps and Magisk.
https://github.com/pagkly/MagiskOnWaydroid
I then downloaded RootExplorer and tried mounting the root and /system directories as read-write, which worked. However, the shell on the host system didn't seem capable of doing this.
As someone used to working with the shell, relying solely on a GUI for operations felt inconvenient. If RootExplorer could obtain read-write permissions for these paths, why couldn't the shell?
After some more Googling, I found many answers (including on XDA):
All pointing to this website:
https://www.systemrw.com/download.php
Although the author's colorful, flashy fonts and some quirky memes were annoying, following the steps actually solved my urgent problem.
Additionally, this answer helped resolve the communication issue between the host and Waydroid:
https://www.reddit.com/r/waydroid/comments/13e619n/how_do_i_write_to_waydroid_files_from_arch_linux/
So, all the work I've done so far is essentially what could have been achieved in the Android 4 era with a simple one-click root tool. It seems Android's security barriers have indeed improved significantly.
waydroid + magisk + Xposed
I found an Xposed installer online, but the resource fetching URL repo.xposed.info stopped working a year ago.
https://forum.xda-developers.com/t/is-there-a-problem-in-xposed-website.4472673/
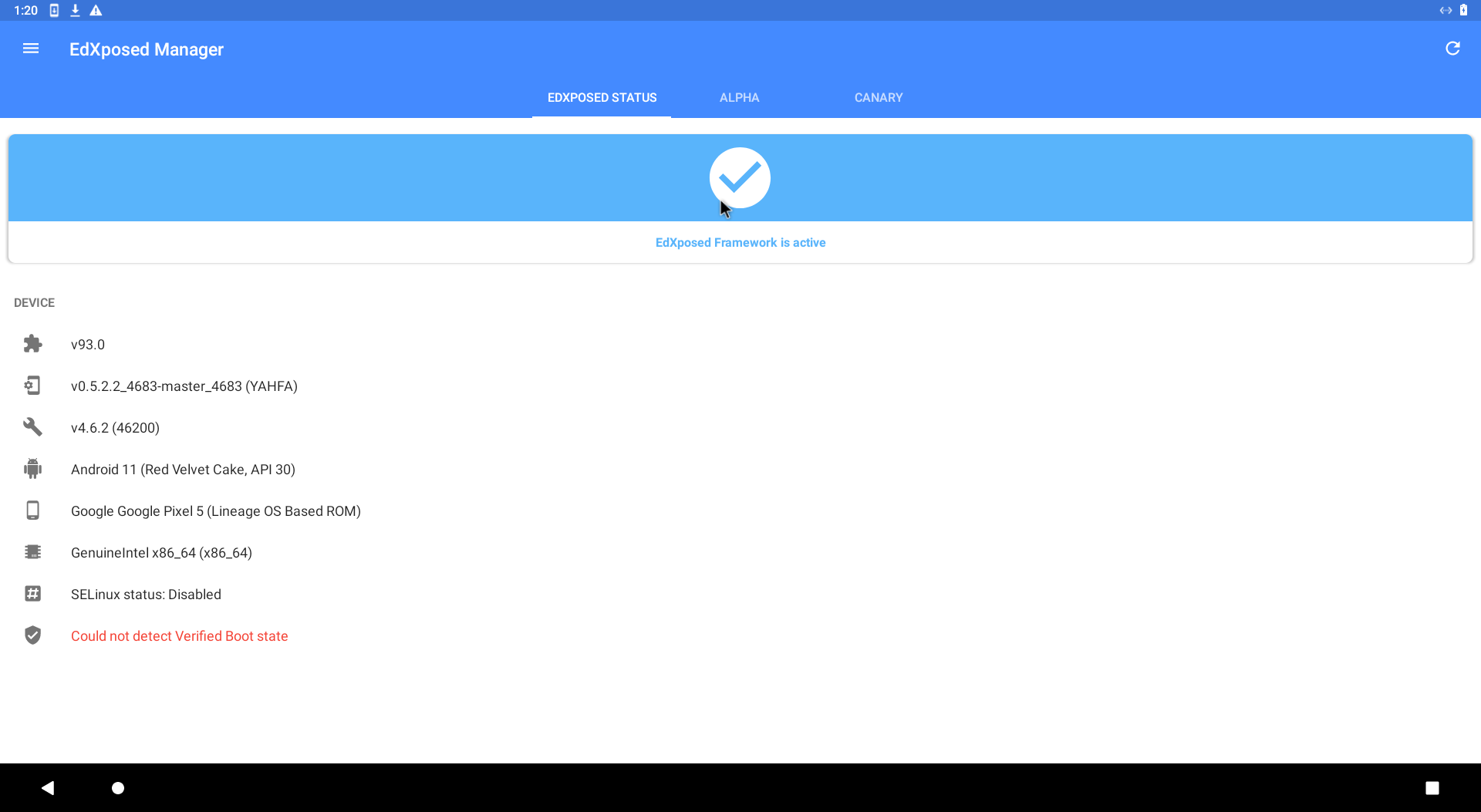
waydroid + magisk + EdXposed
So I found another alternative, EdXposed.
https://github.com/ElderDrivers/EdXposed
At first, I didn't realize that the EdXposed framework needed to be installed through Magisk, which left me stuck for a while. Then, when trying to load the zip via Magisk, I ran into an unzip error. I found this forum post:
https://forum.xda-developers.com/t/magisk-module-unzip-error.4503395/
The issue was that the downloaded zip file shouldn't be wrapped inside another folder (which reminded me of the submission method from the long-forgotten nand2tetris course).
Finally, I got EdXposed installed. It was 2 a.m., and four hours had passed since I started.
waydroid + magisk + EdXposed + ProxyDroid + burpsuite
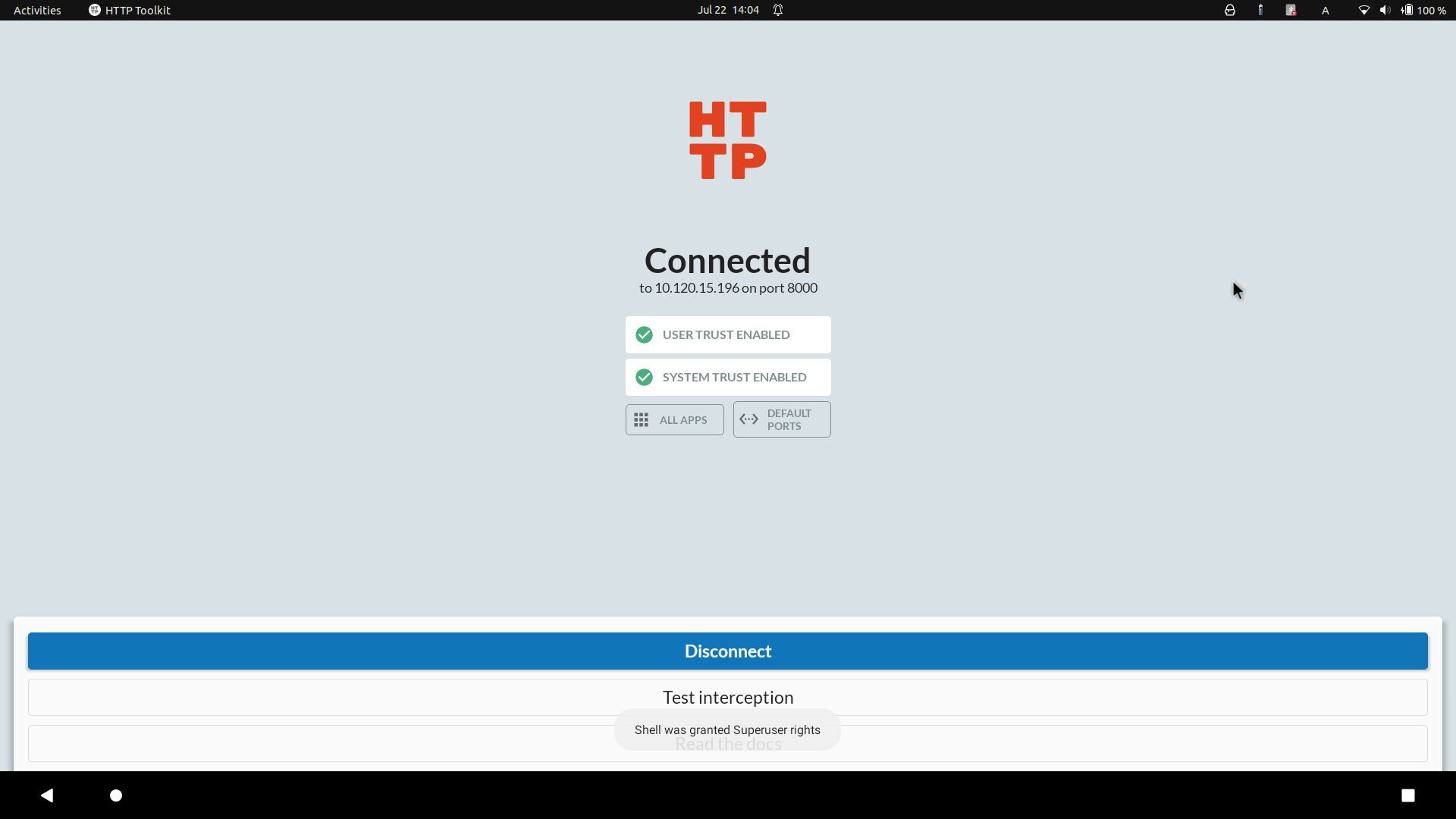
Since httptoolkit only provides a QR code scanning method for the Android side, and Waydroid does not support the camera, this option is temporarily not considered.
Additionally, Waydroid does not support Wi-Fi and cannot be configured with a proxy. Even if you set http_proxy in the shell, it only affects commands like curl and wget within the shell and does not support HTTPS.
Therefore, I tried using ProxyDroid to route all apps through Burp Suite's proxy address, but it had no effect.
After some research on Google, the possible reason is that some apps inherently do not support proxies, so even setting a global proxy at the root level may not work.
waydroid + magisk + EdXposed + PCAPdroid
While translating the answers to the question above, one response speculated that we might be looking for packet capture tools on the Android platform (you really are good at guessing), and recommended PCAPDroid.
However, PCAPDroid's HTTPS packet capture is an experimental feature and doesn't seem very stable. After following its guide to install PCAPDroid mitm and the relevant certificates, I still couldn't capture HTTPS packets.
Then I remembered the previously mentioned Xposed module JustTrustMe. After installing it, there was no change at all.
After searching for alternatives on Google, I found TrustMeAlready:
https://github.com/ViRb3/TrustMeAlready
This time, when testing browser access to Google, I managed to capture some HTTPS packets.
But there was bad news: the Grab app wouldn't open. Although a possible solution might be MagiskHide, I felt like I was nearing the end of this road, so I decided to try another approach.
android + apk-mitm + httptoolkit(user)
Why not directly instrument the APK? This led to the following solution:
https://github.com/shroudedcode/apk-mitm
Since Grab couldn't be used in Waydroid anymore, I directly installed the patched Grab on my own phone. I expected some obstacles during the installation of a self-signed app, but surprisingly, it installed without issues.
Next, I used httptoolkit again, and indeed, it captured far more HTTPS packets than before. However, I encountered a minor issue:
- When redirecting from Grab's website to BOC, if packet capture (mitm) was detected, the redirection would fail.
- But if I successfully entered BOC's website, I could freely capture packets. However, the page couldn't be refreshed, making it impossible to obtain the URL.
This issue was eventually resolved as follows:
Android + apk-mitm + httptoolkit(user) + a bit of luck
First, disable httptoolkit's intercept, then open the BOC link. Wait 0.5 to 1 second before enabling intercept again.
With a bit of luck, you'll enter the BOC page. At this point, you can retrieve the BOC login page URL from the response of a certain GET request that fetches the redirect link. This page can only be opened using a mobile user agent:
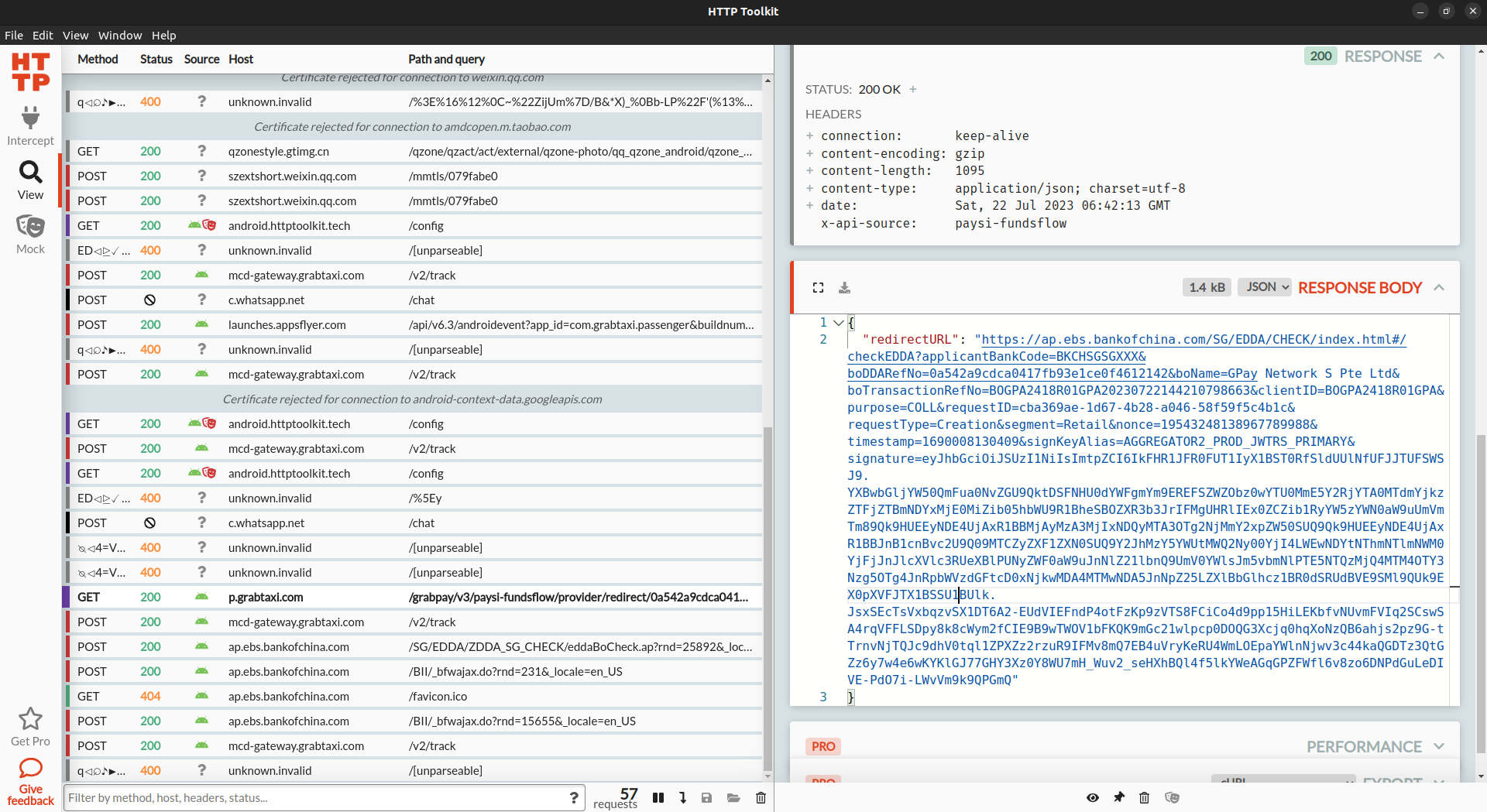
It was already 4 AM at this point—time to clock out.
Afterword
- The last time I worked with Xposed was two years ago. That post is now buried in the dustbin of history.
I originally intended to dig it up, but since it wasn't on a physical device, I decided to wait until I needed to set up a soft router.So, in 2025, I ended up using the same phone again to solve an app packet capture issue. The details can be found here. - After raising an issue with the httptoolkit author, I learned that Waydroid actually supports ADB. I finally got to see the two coveted green checkmarks:
- Even with magiskhide installed, it seems there are still issues with Grab:
:/ # magisk --denylist ls
com.google.android.gms|com.google.android.gms.unstable
com.grabtaxi.passenger|com.grabtaxi.passenger
:/ # pm list | grep grab
1|:/ # pm list packages -f | grep grab
package:/data/app/~~oaJzpweAfnANsOwMdRVm8g==/com.grabtaxi.passenger-8U-wrhDH8uhWC6LSRS11cg==/base.apk=com.grabtaxi.passenger
:/ #